Welcome to OpenConnect graphical client pages. OpenConnect is a VPN client, that utilizes TLS and DTLS for secure session establishment, and is compatible with the CISCO AnyConnect SSL VPN protocol. OpenConnect-gui is the graphical client of OpenConnect for the Microsoft Windows system (or any other system Qt and OpenConnect run at). The client is currently at beta testing phase. 在VPN会话期间,在VPN会话期间,我们的系统会跟踪活跃会话 - 连接时间、IP地址、设备类型和Astrill VPN应用程序的版本。一旦您从VPN断开连接,我们的系统将永久删除此信息。此信息仅用于限制同时从单个帐户连接的设备数量。. Openconnect is used to access virtual private networks (VPNs) which are compatible with the Cisco AnyConnect SSL VPN protocol. With this tool you can securely connect remotely to your work place. Split tunneling with openconnect - A guide on how to use openconnect to establish a vpn connection to an enterprise cisco anyconnect vpn endpoint with client side routing. vpn-openconnect-connect-to-cisco-anyconnect.md.
OpenConnect is a client for Cisco's AnyConnect SSL VPN and Pulse Secure's Pulse Connect Secure.
Installation
Install the openconnect package.
Usage
See openconnect(8). Simply run openconnect as root and enter your username and password when prompted:

More advanced invocation with username and password. Input the password after running the command.
Often VPN providers are offering different authentication groups for different access configurations like for example for a full tunnel or split tunnel connection. To show the different offered auth-groups and to get more information about the connection to the server in general use:
Sometimes, connecting to a Cisco VPN, the CSD (Cisco Secure Desktop) mechanism is required (see: https://www.infradead.org/openconnect/csd.html). In that case using the '--csd-wrapper' parameter can help, the wrappers are stored under '/usr/lib/openconnect/'.
Juniper Pulse Client
In order to connect to a Pulse Connect Secure server you need to know the SHA-1 of its certificate.
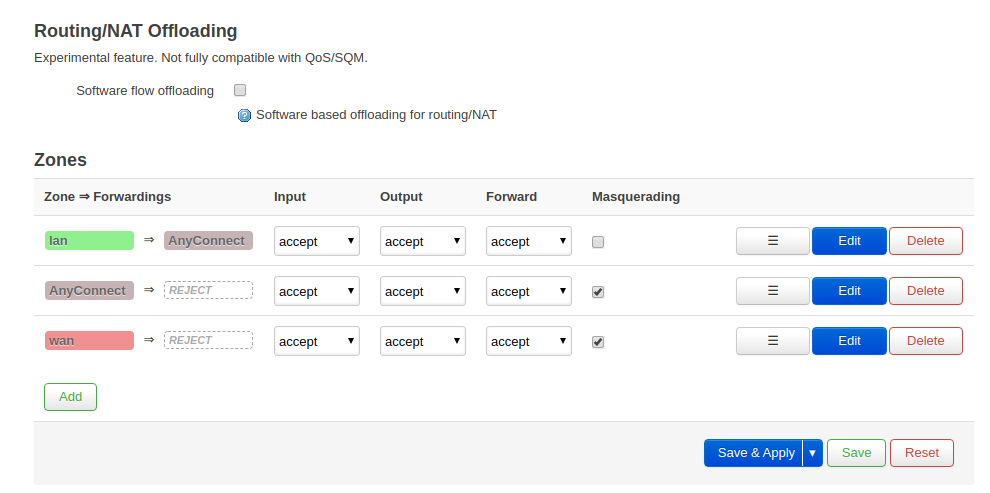
Split routing
Split routing can be achieved using vpn-slice-gitAUR in place of vpnc-script, so that you can selectively access hosts over the VPN but otherwise remain on your own LAN. Example:
Integration

NetworkManager
Install the networkmanager-openconnect package, then restartNetworkManager.service.
Configure and connect with nm-applet (NetworkManager's icon tray utility from network-manager-applet) or similar utility.
See NetworkManager for details.
netctl
Openconnect Cisco Vpn Client
A simple tuntapnetctl.profile(5) can be used to integrate OpenConnect in the normal Netctl workflow. For example:
This allows execution like:
Note that this relies on LOCAL_USERNAME having a gpg-agent running, with the passphrase for the PGP key already cached.
If pass’ interactive query is wanted, use the following line for PASSWORD_CMD:
Adjust the DISPLAY variable as necessary.
Problem
I needed to maintain a continuous (or near-continuous) VPN connection to a server (server 1) from another server (server 2) that was running a Tomcat web-app (on Ubuntu Server 16.04). Server 1 was part of a network which provides secured VPN access to external connections via Cisco Anyconnect.
Solution
Users have reported that this approach does not work with newer version of openconnect etc.
Given I haven't attempted this approach (nor have need of it) I am just leaving this here for historical purposes (or something that did work previously).
For this, we're going to use the excellent OpenConnect to connect to server 1, and a bash script to continuously check the connection, and if disconnected, to reconnect.
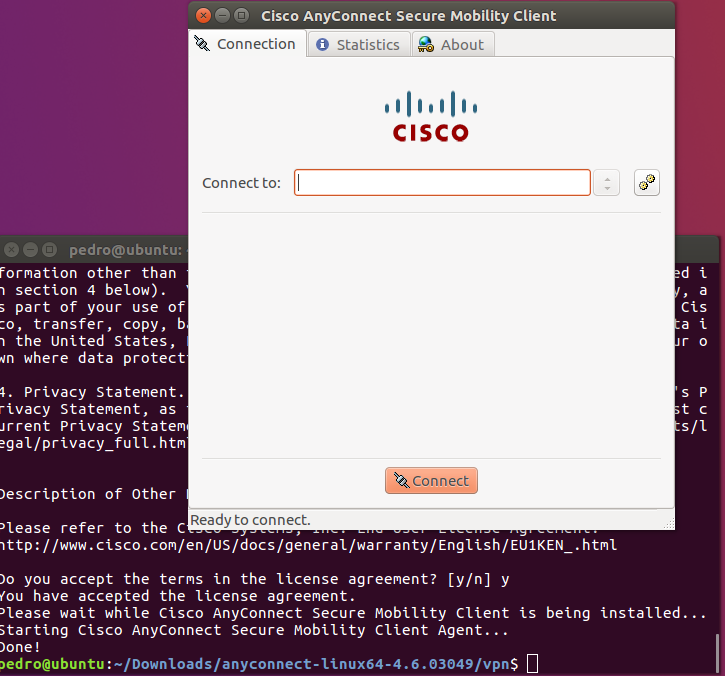
Install OpenConnect
Let's first install OpenConnect. Server 2 was running Ubuntu 16.04. Let's do:
Creating a script to reconnect when disconnected
Please note that the below approach stores a vpn password in clear text in the script file, and as such is a potential security risk. The script should be locked down to stop users without authorisation from viewing its contents. Hence, this approach may only be appropriate for a server/system that is strictly managed or not accessed by other users.
Let's create a script that will:
Openconnect Cisco Vpn
- connect to your VPN;
- check every
xseconds whether it is still connected - reconnect to the VPN if the connection is broken
In the below example we'll create a vpn.sh script.
Copy the following into in your script:
Let's at least lock this file down to be only readable by root:
Running script in background
Once your happy with your script you can run said script as a background script:
Stopping background script
To stop/disconnect the VPN and script, use ps to find the PID's of the VPN script and the openconnect process by:
For example, on my system, running the above gives:
I would kill PID's 10525 and 28445, like this:
Split tunnelling with vpn-slice
Split tunnelling allows you to explicitly define the ip address(es) for which traffic will be routed to on the vpn server side. This is useful for situations where you might want to route traffic to/from a specific ip, and want all other traffic to use normal (non-vpn) connections.
For this use case you can use vpn-slice. Once installed (see here for requirements and install guide), you can then modify your the script above as follows (see line 15 for the vpn-slice script argument):
where <IP-ADDRESS> is the ip address (or addresses, separated by a space) is what addresses you want tunnelled to the vpn.
NOTE: you should install vpn-slice with sudo to ensure it is available on the standard path (otherwise you'll need to give the full path to the vpn-slice script).
References
Related articles
Openconnect Cisco Vpn Client
- Page:
